IT Skills Security Security Accreditations and Best Practice Certified Ethical Hacker (CEH) v10
Explore how Security Incident and Event Monitoring (SIEM), User Behavior Analytics (UBA), and Access Control Lists can be used to prevent data loss or leakage.
| Objectives |
|---|
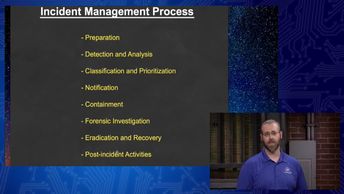
CEHv10: Security Controls Part 2
|