IT Skills Security Security Accreditations and Best Practice Certified Ethical Hacker (CEH) v10
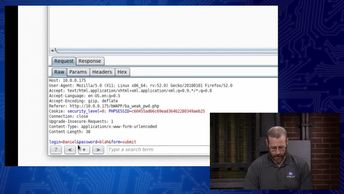
Discover attacks against web apps using weak or broken authentication methods, and how cross-site scripting can be used to execute code. This course will help prepare you for the 312-50: Certified Ethical Hacker v10 exam. Watch these videos and learn how to identify attacks that can exploit weak authentication methods, identify methods to protect against data leaking, recognize the potential dangers of poor encoding practices, identify the types of cross site scripting (XSS) and associated vulnerabilities, recognize potential dangers inherent in running web applications, and mitigate the dangers of using Indirect Object References (IDOR) in web applications.
| Objectives |
|---|
Certified Ethical Hacker - CEHv10: Common Web App Threats Part 2
|