IT Skills Security Security Accreditations and Best Practice Certified Ethical Hacker (CEH) v10
Examine cryptography concepts such as cryptosystems, hashing algorithms, digital signatures and certificates, and key wrapping, as you prepare for the 312-50: Certified Ethical Hacker v10 exam. Watch these videos and learn how to identify examples of Asymmetric Algorithms. Find an additional name for Message Digests. Learn the basic requirements of a hash function. Recognize the primary purposes of Public Key Infrastructure. Find critical information in a Digital Certificate. Recall the phases of the certificate lifecycle, and finally, identify the RFC 2048 requirements for ISAKMP.
| Objectives |
|---|
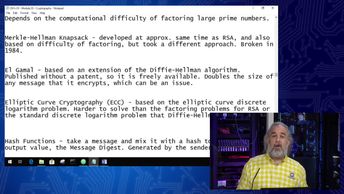
Certified Ethical Hacker - CEHv10: Cryptography Concepts Part 3
|