IT Professional Curricula Internet and Network Technologies Solution Area Security Solutions Certified Ethical Hacker (CEH) v10 (Update)
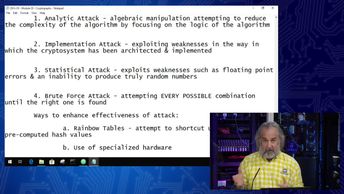
Discover various approaches that can be used to attack a cryptographic system, such as analytic, implementation, brute force, ciphertext only, meet in the middle, and replay attacks. This course will help prepare for the 312-50: Certified Ethical Hacker v10 exam. In this video, you will compare techniques used to attack a cryptographic system, identify differences between different types of attacks against a cryptographic system, and identify likely vulnerabilities to different attacks against a cryptographic system.
| Objectives |
|---|
Certified Ethical Hacker - CEHv10: Cryptography Attacks
|