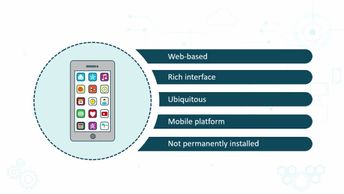
Explore security architecture considerations such as control identification and prioritization, distributed computing, cloud architectures, mobile applications, and hardware platform concerns in this 12-video course. First, learn to identify characteristics of control identification, or an organization's security controls in an enterprise setting and how to prioritize and enterprise's existing security controls. The course then examines the elements of distributed computing, a type of parallel computing in which software is divided into multiple tasks. Next, learners will explore service-oriented architecture, which is a collection of services that communicate with each other. You will learn about rich Internet web-based applications and pervasive computing, including the Internet of Things, wireless and sensor networks, embedded security architecture, cloud architectures, mobile app architectures, and hardware platforms. Finally, the course explores how an embedded system is designed to perform a specific operation as part of a larger hardware-based machine or system. This course can be used in preparation for the (ISC)2 CSSLP: Certified Secure Software Lifecycle Professional certification exam.
| Objectives |
|---|
Certified Secure Software Lifecycle Professional (CSSLP) 2019: Security Architecture
|